#4: AI Incident Response Orchestrator (The Top 10 Emerging AI Security Roles)
You use defensive AI agents for direct combat against adversarial agents within your network infrastructure. This is agents versus agents, automated warfare.
These roles reflect current market studies, desired competencies, and evolving security threats, and are the result of two years of industry tracking. The focus: defending the nation’s new AI technological capabilities. These roles align with the national push for AI incident response and a skilled cyber workforce.
Next up in our list of Ten Emerging AI Security Roles:
4. AI Incident Response Orchestrator
Market: Rapidly expanding field
You use defensive AI agents for direct combat against adversarial agents within your network infrastructure. This is agents versus agents: automated warfare where your defensive swarms repair and remediate systems as fast as adversaries infect them.
The new battlefield: Attackers entering your network with AI agents move too fast for human response teams. Your defensive agents operate independently to hunt adversarial code, halt attack sequences, and restore damaged systems at speeds surpassing traditional malware spread.
Why this role exploded: The January 2024 Arup deepfake incident revealed traditional incident response inadequacy for AI-enhanced attacks1. Threat actors staged multi-participant video conferences with deepfakes replacing all attendees except the targeted victim. Unit 42 research showed AI integration speeds ransomware deployment dramatically, achieving complete network breaches within minutes2. The old "we have 72 hours to respond" playbook now looks as outdated as a fax machine.
Organizations take much longer to identify and contain AI breaches compared to traditional breaches3. When attackers move at machine speed, human-speed responses become academic exercises in futility.
Agent combat orchestration:
Implement defensive AI agents detecting and eliminating adversarial agents in real time
Deploy repair swarms working faster than attacks can expand to rebuild compromised systems
Execute agent-to-agent combat where defensive systems fight attacking AI directly
Adapt containment agent tactics based on observed adversarial actions
Command healing agents maintaining network functionality during ongoing battles
Next in this series, I’ll share more on each of the these emerging AI security roles:
AI Cybersecurity Careers: The Complete Guide
Success requires more than technical knowledge. Rapid change makes continuous learning mandatory.
Rob T. Lee | Chief of Research and Chief AI Officer, SANS Institute
Follow me on LinkedIn | X | TikTok | YouTube
For SANS AI Security training and thought leadership, click here
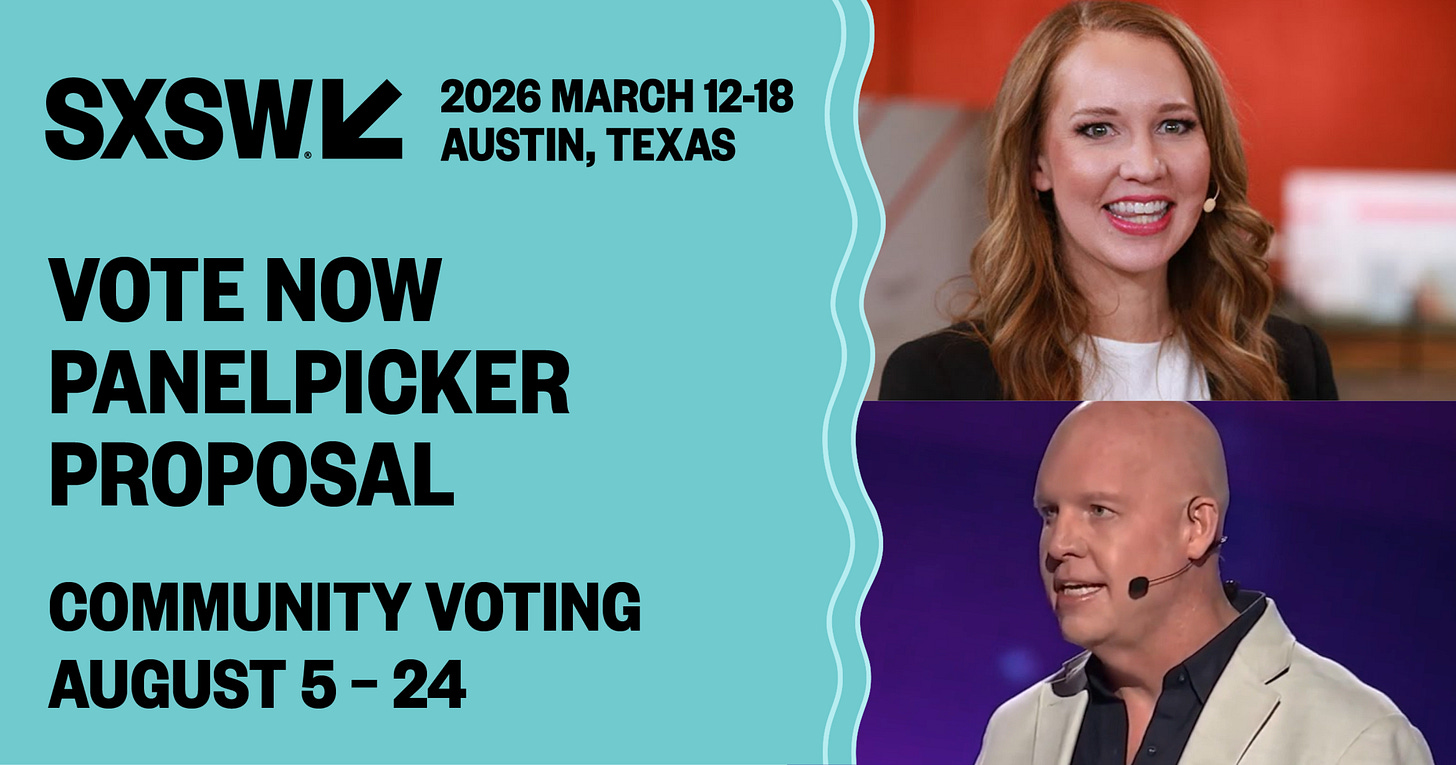
SXSW 2026: We need your vote! Put Wendi Whitmore and me on the SXSW stage for a candid discussion on AI security with the business, tech, and innovation community: 25 Minutes to Breach: The Future of AI-Powered Cybercrime
It takes less than a minute to vote:
- Log in (or sign up) at SXSW
- Click the heart next to the title, 25 Minutes to Breach: The Future of AI-Powered Cybercrime.
Thank you for your support!
Have you submitted your nomination for this year’s Difference Maker Awards? Nominations are open NOW.
Palo Alto Networks Unit 42: https://unit42.paloaltonetworks.com
IBM Security: https://www.ibm.com/security
IBM Cost of a Data Breach Report 2025: https://www.ibm.com/reports/data-breach